Access Control
Full control over who access what
We make it easy to apply the security policies and permissions your organization need. With MobilityGuard OneGate granular access control you can place your specific limitations on who can get into your organization’s system.
You can control where, when and how they can access it and what they can do with it. For example, a security policy can be defined by group, source IP & network, authentication method, encryption grade, URL path, date & time.
Challenges
![]() Insecure password routines
Insecure password routines
![]() Lack of visibility into who has access to what
Lack of visibility into who has access to what
![]() Insecure management of partners’, customers’ and contractors’ permissions
Insecure management of partners’, customers’ and contractors’ permissions
![]() Company growth with critical scaling challenges
Company growth with critical scaling challenges
![]() Time consuming for IT team resulting in slow action
Time consuming for IT team resulting in slow action
![]() High costs of maintenance
High costs of maintenance
MobilityGuard’s solutions
![]() Solves the identification puzzle
Solves the identification puzzle
![]() Full control over who access what – where, when and how Flexible: different methods for identification for different access situations
Full control over who access what – where, when and how Flexible: different methods for identification for different access situations
![]() Access to more than 15 secure, built-in authentication methods
Access to more than 15 secure, built-in authentication methods
![]() Easy to change, add and remove permissions
Easy to change, add and remove permissions
![]() Scalable solution
Scalable solution
![]() Cost effective
Cost effective
Granular access based on the authentication method used
Granular permissions are used to construct site-specific roles with privileges to match your requirements, and restrict system administrators from accessing user data. MobilityGuard OneGate protects your organization by granular access controls.
Traditionally access levels are based on how strongly the user has been identified – this works rather like an on and off switch. If appropriately identified, the user has access to the entire network. However, MobilityGuard OneGate helps you to differentiate access levels based on how strongly the user has been identified. It includes a mechanism for giving granular access to any system based on a policy set, which ranks the methods used for identification. In practice this means that if the user is identified with a stronger authentication method then they will automatically have access to a wider set of applications.
Access control with no additional hardware or software
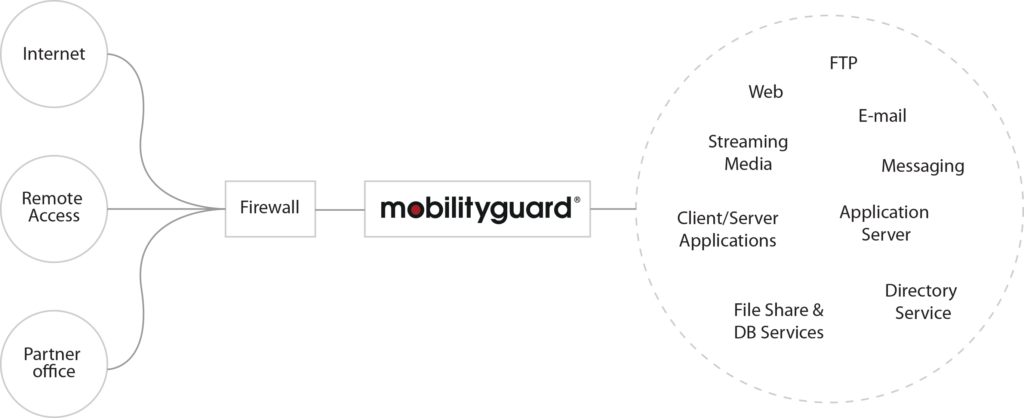
MobilityGuard builds a gateway that allows authorized users to securely access all types of sensitive internal systems and information, irrespective of time and place. A gateway that prevents hostile code from reaching your network.
Relevant links
Read more about relevant product or case – or contact our sales department directly who will guide you to the right secure solution matching your needs.

